Looking for an overview on securing your Amazon AWS infrastructure? Go here.
The virtual scanner appliance allows scanning in Amazon EC2-Classic and EC2-VPC. Learn more
If this is your first EC2 scan, then we recommend you start by creating an EC2 connector. You create EC2 connectors within the AssetView application. A wizard will walk you through the steps for selecting EC2 hosts to scan. Learn more
There are recommended steps you'll want to take before starting your scan, including configuring your virtual scanner appliance and making sure it's connected, defining API proxy settings, configuring security groups and setting up OS authentication. See the checklist
You'll need to reach out to your Qualys TAM or Qualys Support to request access to a) GovCloud Feature and b) Qualys Virtual Scanner Appliance AMI. Then you'll follow the scan steps below. Learn how to get started
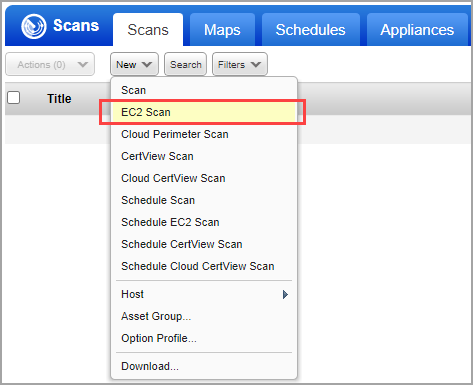
Go to Scans > Scans > New > EC2 Scan (or Schedule EC2 Scan). Click here for help with scheduling.
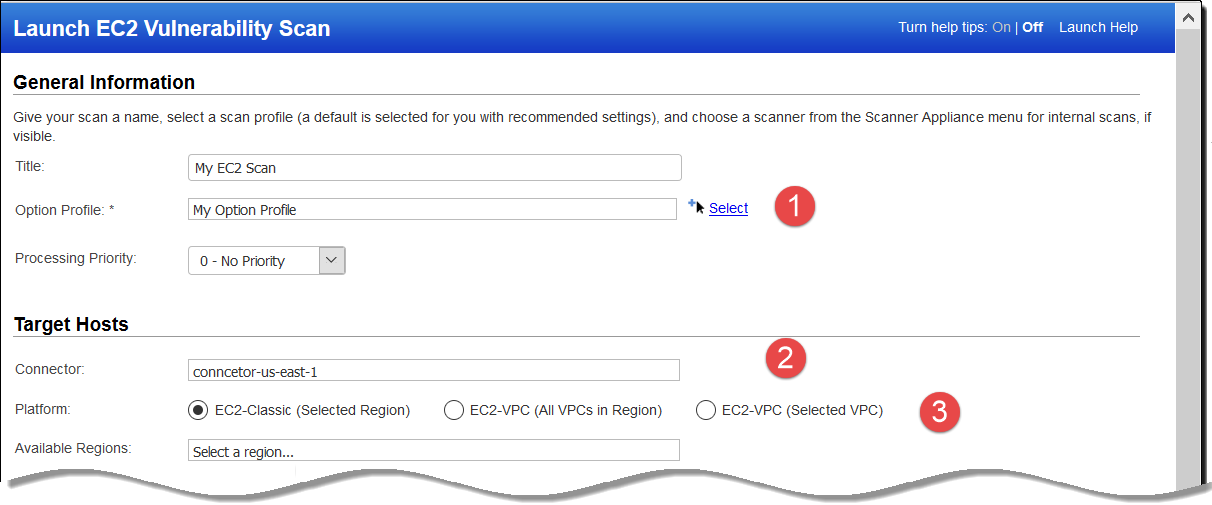
Provide scan settings:
(1) Give your scan a title and select the option profile you configured with authentication.
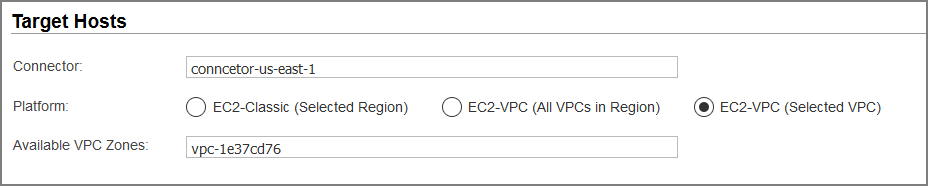
(2) Select the EC2 connector name you've configured.
(3) Choose one of these platform options: EC2 Classic, EC2 VPC (All VPCs in the region) or EC2 VPC (Selected VPC). Based on your selection, you’ll select the region(s). Click here for help choosing an option.
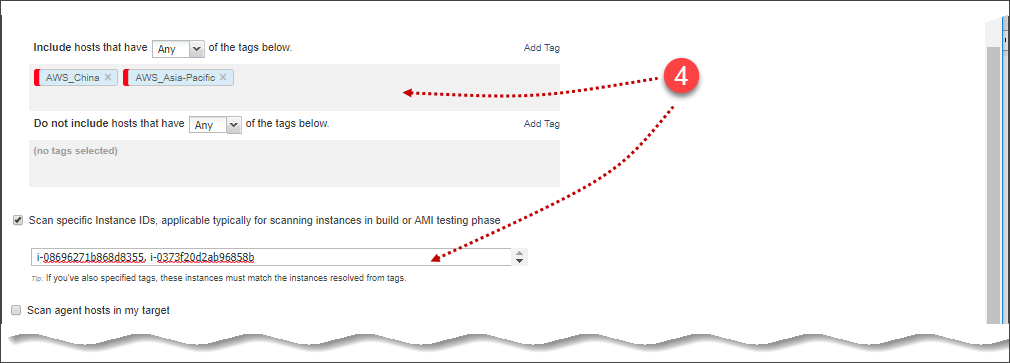
(4) Select asset tags to specify the EC2 hosts to be scanned. These are the assets activated for your connector.
Optionally, scan specific EC2 instance IDs. Instance IDs can be specified with or without asset tags. To specify instance IDs, select "Scan specific Instance IDs, applicable typically for scanning instances in build or AMI testing phase" and enter the instance IDs in the field provided. When the scan is launched, we'll check if the instance IDs you entered are valid. If at least one instance ID is valid, the scan will continue on the valid instance IDs, and any invalid instance IDs will be skipped. We'll list invalid instance IDs and the reasons they are considered invalid on the Scan Preview page. If none of the instance IDs you entered are valid, you'll get an Error.
(5) Choose the Virtual Scanner Appliance AMI you’ve launched in Amazon EC2.
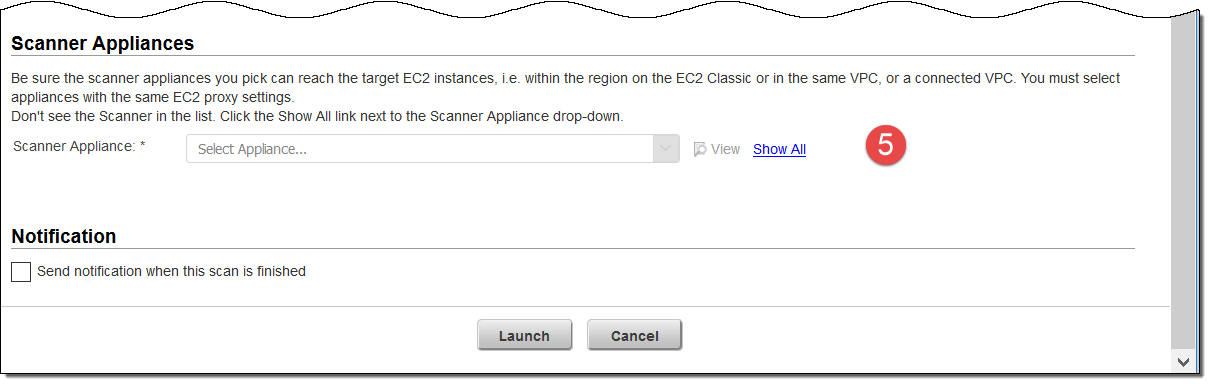
Click Launch and start scanning and securing your Amazon EC2 infrastructure.
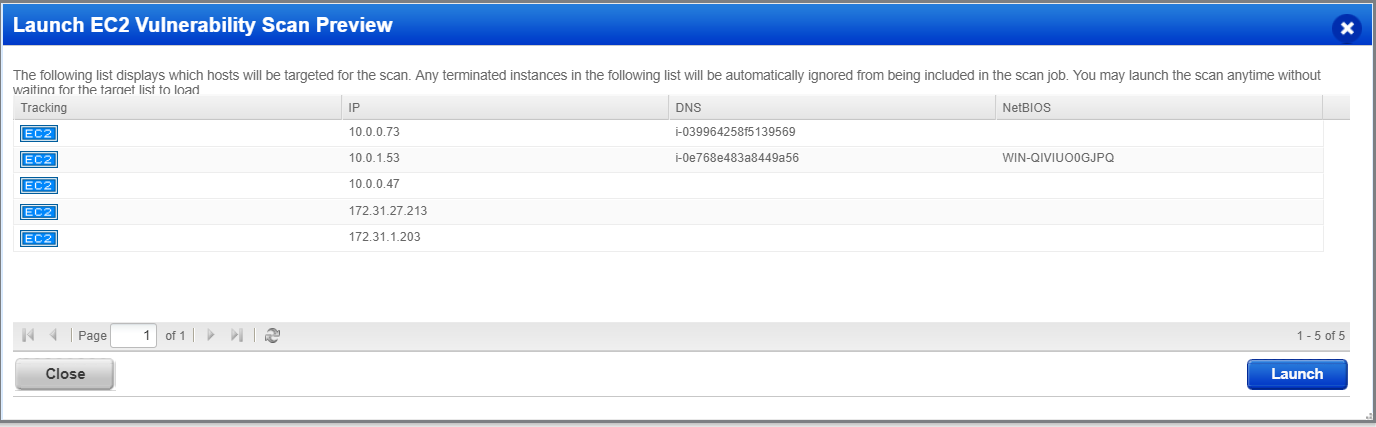
The EC2 Vulnerability Scan Preview lists all the instances (including terminated). The terminated instances will be ignored from the scan and filtered out during the scan.
Create reports to identify the vulnerabilities on your EC2 assets. Go to Reports > Reports > New > Scan Report. You can then choose a pre-configured template or customized template. Give the report a name, choose the template, report format, hosts (IP address or tags), and generate the report.
Depending on your template settings, your report could include graphs, charts depicting vulnerability information and EC2 instance information such as Image Id, VPC Id, Instance state, type and so on. You could use the instance information for remediation.
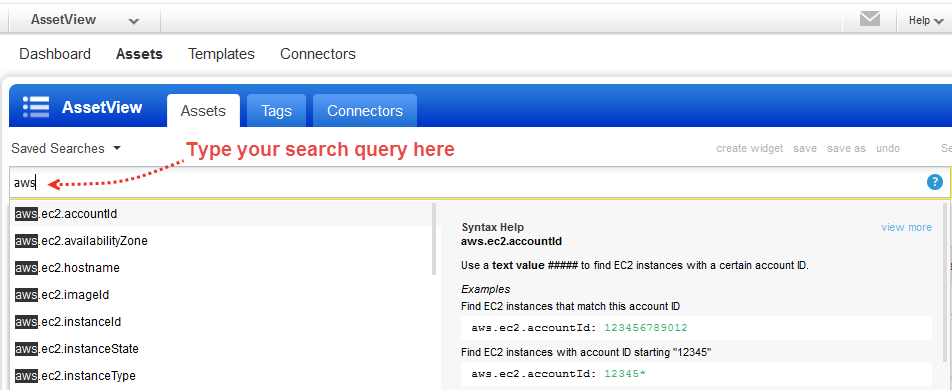
Our search capabilities allow you to find all about your assets all in one place.
Choose AssetView from the app picker. Go to the Assets tab. Start typing AWS, and we'll show you the asset properties you can search like accountId, instanceType, hostname, etc. Select the one you're interested in.
Choose EC2 Classic (Selected Region) to scan EC2 classic hosts in a region. When selected, we’ll only scan EC2 Classic instances in the region.
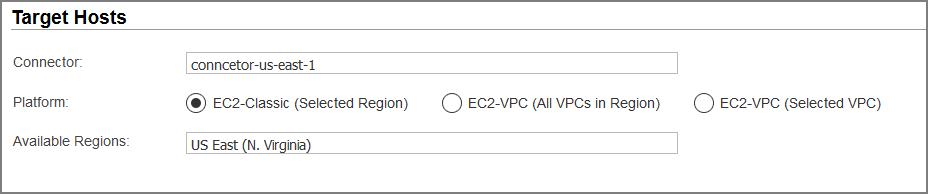
Choose EC2-VPC (Selected VPC) to scan only a VPC you select.
Choose EC2-VPC (All VPCs in Region) to scan all VPCs in a region. Select this option ONLY if there is peering between all the VPCs in the region, or you could end up with Host not found errors for instances where your Virtual Scanner Appliances cannot reach them.
